Direction: E-UTRAN => UE
Signalling Radio Bearer: SRB1
RLC Mode: AM
Logical Channel: DCCH
Transport Channel: DL-SCH
The SECURITY MODE COMMAND message is used to command the UE for the activation of AS security. E-UTRAN always initiates this procedure prior to the establishment of Signalling Radio Bearer2 (SRB2) and Data Radio Bearers (DRBs).
AS security comprises of the integrity protection of RRC signalling (SRBs) as well as the ciphering of RRC signalling (SRBs) and user plane data (DRBs). The integrity protection algorithm is common for signalling radio bearers SRB1 and SRB2. The ciphering algorithm is common for all radio bearers (i.e. SRB1, SRB2 and DRBs). Neither integrity protection nor ciphering applies for SRB0.
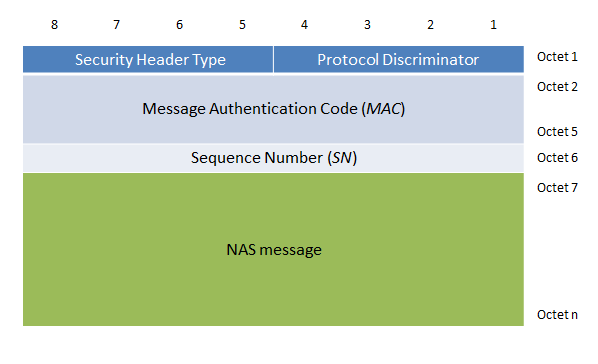
The eNodeB sends integrity protected SECURITY MODE COMMAND message to the UE. The UE shall derive KeNB and KRRCint which is associated with integrity protection algorithm indicated in the SECURITY MODE COMMAND. Then, UE verifies the Integrity of the received SECURITY MODE COMMAND by checking the Message Authentication Code (MAC) in the SECURITY MODE COMMAND message. If the SECURITY MODE COMMAND message fails the integrity protection check, then the UE sends SECURITY MODE FAILURE to the eNodeB.
If the SECURITY MODE COMMAND passes the integrity protection check, then the UE shall derive the encryption keys KRRCenc key and the KUPenc keys associated with the ciphering algorithm indicated in the SECURITY MODE COMMAND.
The UE shall apply integrity protection using the indicated algorithm (EIA) and the integrity key, KRRCint immediately, i.e. integrity protection shall be applied to all subsequent messages received and sent by the UE, including the SECURITY MODE COMPLETE message.
The UE shall apply ciphering using the indicated algorithm (EEA), KRRCenc key and the KUPenc key after completing the procedure, i.e. ciphering shall be applied to all subsequent messages received and sent by the UE, except for the SECURITY MODE COMPLETE message which is sent un-ciphered.
Example: Security Mode Command
More details about the security architecture and different kinds of keys are explained here
Reference: 3GPP TS 36.331 and 3GPP TS 33.401